We recently deployed RPKI invalid == reject! on our eBGP Routers after RPKI Validation was already enabled for about one year with Local-Pref 10 for invalids. To fulfill the purpose of RPKI and help to make the internet a more secure place someone must start to deploy those security mechanisms. I hope we see a lot more networks to follow in future.
Following for example bgpstream on Twitter you get an idea how many hijacks are created day per day by intention or on human error. Help to prevent installing those on your tables (if RPKI is enabled for those prefixes) is quite easy:
First of all one would need a working RPKI Validator. RIPE provides a good one which is easy to install: https://www.ripe.net/manage-ips-and-asns/resource-management/certification/tools-and-resources
Routers will need a Connection to the Validator to get the database:
routing-options validation
group rpki-validator {
session x.x.x.x {
refresh-time 120;
hold-time 180;
port 8282;
local-address x.x.x.x;
}
}
Check if connection works:
show validation session Session State Flaps Uptime #IPv4/IPv6 records x.x.x.x Up 0 66w0d 10:49:31 45816/8263show validation database
To get our routes checked and apply the validation-state / reject the invalids we create a policy which can be added to our BGP Peer(s) Import statement:
show policy-options policy-statement rpki
term validation {
from {
protocol bgp;
validation-database valid;
}
then {
validation-state valid;
next policy;
}
}
term validationunveri {
from {
protocol bgp;
validation-database unknown;
}
then next policy;
}
term validationinvalid {
from {
protocol bgp;
validation-database invalid;
}
then {
validation-state invalid;
reject;
}
}
Make sure that iBGP Sessions will exchange the validation states via a community on other routers or import rpki policy on iBGP sessions.
What to expect:
After the deployment you’ll see (depending on peer) about 4700 invalids which will be rejected. About 50% of them are covered by less specifics so you won’t loose connectivity to those. The rest will be dropped but after running the reject policy for about one week we didn’t receive any complaints about reachability issues.
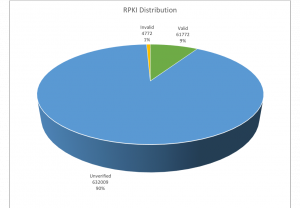
(IPv4 Distribution only), everything works as well for IPv6.
Looking forward that the green piece of cake will grow.
So long 🙂 Get things running!
